In recent weeks, the Israeli spyware program Pegasus and its maker, NSO, were at the center of a firestorm of media reports alleging misuse of this powerful tool by clients. However, another Israeli cyber company that delivers advanced cyber defenses worldwide tends to maintain a much quieter media presence.
Assac Networks protects smartphones from both hacking and tapping, and the fact that it does both at the same time (a rarity in the market) has made it a “go-to” cyber-defense provider for security forces, government and defense organizations, and companies worldwide.
Banks, fintech companies, cell-phone providers and government clients spanning Spain, Singapore, Mexico, Italy and many other states are among Assac’s clientele.
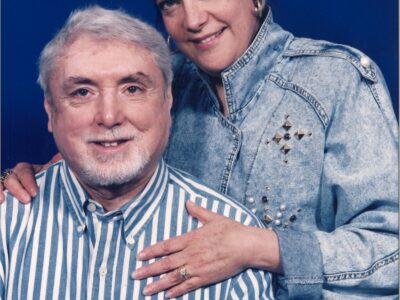
Shimon Zigdon, an encryption expert with 25 years of experience in the telecommunications security sector, founded the company and serves as CEO.
“For all of my adult life, I have dealt with encryption,” Zigdon, who was previously a communications security manager at Elbit Ground Systems, said.
After leaving Elbit in 2012 to set up Assac (which comes from the Hebrew word Hazak, meaning “strong”), Zigdon felt it was time to create a level of cyber defense for phones that could deal with the ever-increasing sophisticated threats.
As Assac’s product spread around the world, it sometimes found itself in the same markets that NSO was operating in, only Assac was selling a powerful cyber shield rather than a sword.
In 2017, Assac carried out a project in Mexico, securing the Mexican Naval Infantry Corps (the Marina), as NSO reportedly sold its spyware to the Mexican military.
As cyber hacking and eavesdropping became more and more advanced, said Zigdon, “I understood that if we don’t step up defenses, there will be no place left for encryption in the space of cyber threats.”
Conventional smartphone defenses are largely irrelevant, he argued, since high-end attackers break into phones “locally,” meaning that they allow the phone to do the deciphering work, and then simply break and enter into the device and steal its information. This can include anything from camera and microphone data, text communication and using the phone as a launchpad to break into company networks.
“As soon as the hack is conducted locally, there is no encryption challenge. It doesn’t matter how well-encrypted the data is on the way to the phone if someone has taken local control of the phone,” he warned.
As a result, Assac focuses on defending what it calls the “endpoint” — the smartphone itself — whether it runs on Android or iOS. “We defend the phone as it was bought, off the shelf. We tell our clients to simply bring their own device,” said Zigdon.
With so many personnel involved in sensitive work using their home devices for work communications, such as email, the need to secure personal phones is more acute than ever.
Zigdon outlined the two main types of threats posed to anyone with a smartphone in their possession: hacking and tapping.
Just as computers come with a range of defenses — from anti-virus programs to firewalls to virtual private networks (VPN) — so, too, do smartphones require an extensive protective shield, he said.
“We know there are a lot of bad actors out there. There are multiple ways for them to take control of a phone — a man in the middle attack [in which attackers can pretend to be a local Wi-Fi server, for example], breaching an operating system or installing malicious applications,” Zigdon said, listing off entry points. “Defending against these attacks is anti-hacking.”
So what exactly is anti-tapping?
Zigdon explains that if an attacker is equipped with a device that can “hijack” a phone’s radio emissions before they reach the intended base station pounces, then that person r is engaged in tapping. This can be done through a “GSM suitcase,” which seizes a local phone’s signal and listens in on it, for example.
The only way to defend against this kind of attack is to encrypt the radio signal before it leaves the phone, so that even if it intercepted “mid-air,” it remains incomprehensible to the eavesdropper, said Zigdon.
“If I take a combination of end-point protection against hacking and tapping, and create an envelope that protects against both, I receive complete protection,” he said.
This, in essence, is what Assac offers its clients around the world.
The target market is not individuals, but rather, companies — often large organizations and often in the defense sector — as well as governments and security services.
“Smartphones are the most vulnerable point in any company’s IT network,” said Zigdon. While company IT managers will always make sure to set up defenses around computers and domains, far too often the need to secure the smartphones used by employees and managers to access the organization’s systems is overlooked.
“An unsecure phone means the entire company system is exposed,” he emphasized.
With any modern smartphone able to track a user’s precise location, record conversations, film surroundings and used to eavesdrop on all forms of remote communication — and be exploited as a gate into organizations’ IT networks—the risks are considerable.
“The only way to disappear from the grid is to throw out your phone,” said Zigdon.
Assac offers two applications to its clients: ShieldiT, available from Google Play and App Store; and ManageiT, which must be operated by an IT manager, tracks the management of the first app.
One of the notorious features of modern hacking patterns is to use tools such as phishing emails to get users to install malicious code on their smartphones by clicking links. But the most advanced spyware programs, such as Pegasus, can do this via a network even without getting the user to click a malicious link.
“As soon as someone makes an attempt like this, Assac will send out an alert. It has an executable program that runs on the phone and constantly checks on the correlation between my phone’s app and what’s taking place on the network. If I open WhatsApp and someone else opens it from another gate, the alert will arrive,” explained Zigdon.
Asked to comment on the NSO controversy storm, which continues to reverberate, Zigdon said that Israel does a thorough job of regulating its defense exports, calling Israeli licensing protocol “the strongest in the world.”
“When NSO set up its system, this was only after it received full authorization for selling abroad for homeland security needs. Israel has lots of technology for attack and also for defense,” he stated. “Assac comes from the world of defense, but our solution is also tightly regulated and subject to the Israeli Encryption Act [that obligates companies that sell encryption technology to receive Defense Ministry authorization].”
He added, “I won’t sell something that will harm national security or which will be unethical.”










Comments